Day 17 of Australian Rail Series
Everyone knows cybersecurity matters. But what if, in rail, the consequences of a breach aren’t measured in data loss — they’re measured in trains that stop, freight that doesn’t move, and passengers in physical danger?
The Story
Everyone knows cybersecurity is important. It protects data. It prevents fraud. It keeps businesses running. These are standard facts, recited in boardrooms and security awareness training sessions around the world.
But what if the standard framing is dangerously inadequate for rail?
In most industries, a cybersecurity breach means data is stolen, services are interrupted, or money is lost. In rail, a cyberattack on signalling systems could cause collisions. An attack on train management systems could halt entire freight networks, disrupting national supply chains. An attack on operational technology doesn’t just create a headline — it creates physical danger.
This is the reversal: rail cybersecurity isn’t an IT problem that happens to involve trains. It’s a safety problem that happens to involve computers. And the rapid digitisation that’s making rail smarter — IoT sensors, cloud analytics, digital signalling, remote monitoring — is simultaneously making it more vulnerable.
The industry is bridging an air gap that kept operational technology safe for decades. The question is whether it’s building a new wall as fast as it’s demolishing the old one.
Day 17 in pictures
A few visuals for the post.
The Deep Dive — 8 Questions
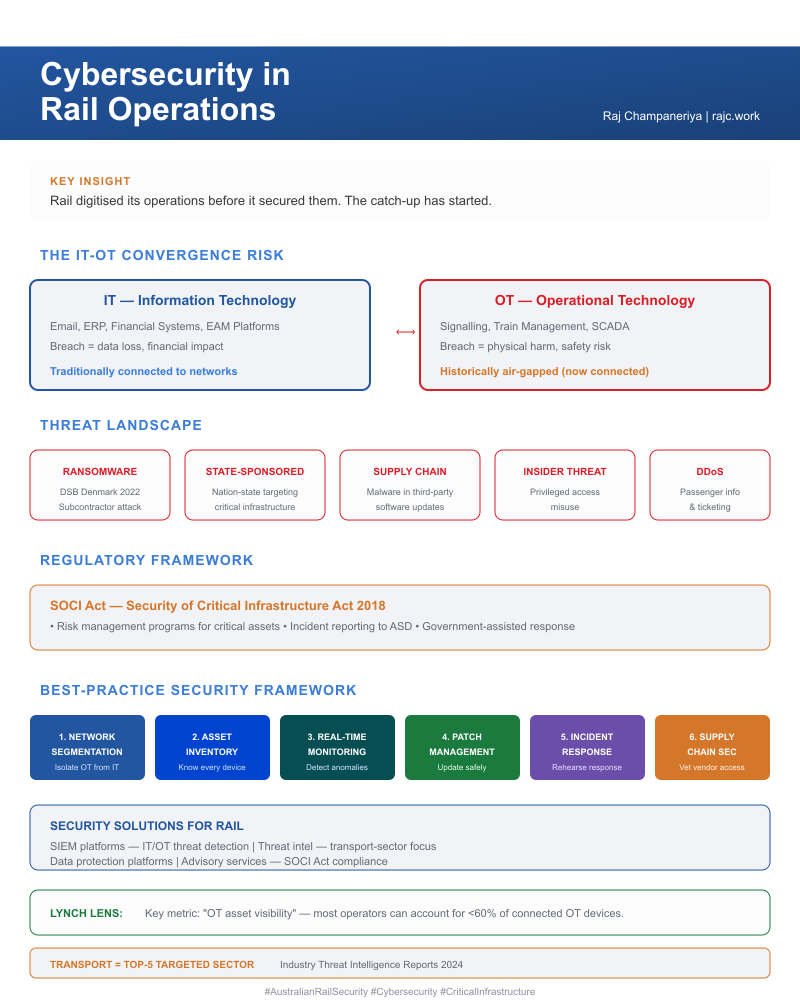
Why does IT–OT convergence dramatically expand the attack surface for critical national infrastructure?
Rail systems are critical national infrastructure. The convergence of two historically separate domains creates the risk:
- IT (Information Technology) — manages business systems: email, ERP, financial systems, Maximo
- OT (Operational Technology) — controls physical processes: signalling, train management, SCADA, track monitoring sensors
Historically, OT was air-gapped — physically disconnected from any network. A hacker couldn’t reach a signalling system because there was no digital path to it.
Digitisation is bridging that gap. IoT sensors on track assets connect to cloud analytics platforms. Remote monitoring systems access operational technology over networks. ETCS digital signalling replaces hardwired systems with software. Each connection creates functionality and vulnerability simultaneously.
How does bridging the air gap create vulnerabilities where none previously existed?
The air gap was crude but effective. No network connection means no network attack. Now consider the modern rail operations centre:
| System | Connected To | Vulnerability Created |
|---|---|---|
| IoT track sensors | Cloud analytics platform | Data interception, sensor spoofing |
| SCADA signalling | Remote monitoring dashboard | Unauthorised access to train control |
| Mobile maintenance apps | Workforce management system | Device compromise, credential theft |
| Digital twin platform | Multiple data sources | Data integrity attacks |
| Passenger information | Internet-facing systems | DDoS, defacement |
Each connection was built for operational benefit. Each also created an attack vector that didn’t exist when the system was isolated. The challenge: capturing digitisation’s benefits while managing the cybersecurity risks it introduces.
Why did the Danish rail attack expose the entire sector’s supply chain vulnerability?
Key threats to rail cybersecurity:
- Ransomware — encrypting operational systems to extort payment. In 2022, a ransomware attack on Danish rail operator DSB’s subcontractor Supeo forced trains to stop because drivers couldn’t access their safety-critical app.
- State-sponsored attacks — targeting critical infrastructure for geopolitical objectives
- Supply chain compromises — malware embedded in third-party software updates
- Insider threats — disgruntled employees with system access
- Denial-of-service — overwhelming passenger information and ticketing systems
The Danish attack was revelatory: the attackers didn’t target DSB directly. They targeted a subcontractor — a pattern the ENISA Railway Cybersecurity report identifies as a growing risk across European rail. The lesson: rail cybersecurity extends beyond the operator’s network to every vendor, supplier, and partner in the digital ecosystem. The Australian Cyber Security Centre (ACSC) classifies rail as a “system of national significance” requiring enhanced security measures, and the CISA TSA Security Directives for surface transportation operators mandate similar supply chain controls in the US.
How does the SOCI Act raise the regulatory bar for rail cybersecurity?
The Security of Critical Infrastructure Act 2018 (SOCI Act, amended 2022) mandates:
- Risk management programs for critical infrastructure assets
- Incident reporting to the Australian Signals Directorate within specified timeframes
- Government-assisted response powers during significant cyber incidents
ONRSR is incorporating cyber risk into Safety Management System requirements — meaning cybersecurity isn’t just an IT compliance issue but a safety obligation. The Australian Government’s 2023–2030 Cyber Security Strategy further raises the bar for critical infrastructure operators.
Non-compliance isn’t just a regulatory risk. It’s a demonstration that the operator hasn’t identified a threat that could physically endanger the people on its network.
Why is network segmentation the foundational first step?
Best-practice cybersecurity for rail follows a layered framework:
| Layer | Purpose |
|---|---|
| Network segmentation | Isolate OT from IT and internet — a breach in one zone cannot spread |
| Asset inventory | Know every connected device and its software version |
| Continuous monitoring | Detect anomalous behaviour on OT networks in real-time |
| Patch management | Update systems without disrupting live operations |
| Incident response planning | Rehearse response to cyber events before they happen |
| Supply chain security | Vet vendor access and software integrity |
This mirrors the NIST Cybersecurity Framework (CSF 2.0) adapted for OT environments, and aligns with the IEC 62443 series — the international standard for industrial automation and control system security. Network segmentation, often implemented using the Purdue Model for industrial control systems, is foundational because without it, every other layer is compromised: a single breach propagates across the entire network.
How can maintainers capture digitisation’s benefits while managing cyber risk?
Every digital enhancement adds a potential vulnerability:
| Digital Enhancement | Operational Benefit | Cyber Risk |
|---|---|---|
| IoT sensors on track | Real-time condition monitoring | Data interception, sensor spoofing |
| Mobile maintenance apps | Paperless work orders | Device compromise |
| Cloud analytics | Predictive maintenance | Unauthorised data access |
| Remote monitoring | Reduced site visits | Unauthorised operational control |
| Digital twin platforms | Asset simulation | Data integrity manipulation |
The answer isn’t to avoid digitisation — it’s to design security into every digital enhancement from the start. Security by design is cheaper than security by retrofit. And in a safety-critical environment, retrofit may come too late.
Why is IBM X-Force’s transportation-sector threat intelligence uniquely valuable?
IBM Security provides a comprehensive rail cybersecurity stack:
- QRadar SIEM — threat detection and response across IT and OT environments
- X-Force threat intelligence — specific to transportation sector attack vectors and threat actors
- IBM Security Guardium — data protection for sensitive operational and passenger data
- IBM Consulting — cybersecurity strategy and SOCI Act compliance assessments
- Managed security services — 24/7 monitoring for operators who lack internal SOC capability
The 2024 X-Force Threat Intelligence Index identified transportation as one of the top-5 targeted sectors for cyberattacks globally. IBM’s OT security expertise — spanning manufacturing, energy, and transport — translates directly to rail’s unique requirements.
Why must rail build cybersecurity capabilities now for threats that are still emerging?
Emerging challenges that today’s defences may not withstand:
- ETCS deployment creates a software-defined signalling attack surface replacing hardwired safety
- Autonomous train operations require impenetrable control system integrity
- Quantum computing threatens current encryption standards that protect rail communications — NIST’s Post-Quantum Cryptography standardisation is racing to provide replacements
- AI-powered attacks become more sophisticated, faster, and harder to detect
- Regulatory requirements continue tightening under SOCI Act amendments
Rail must build cybersecurity capabilities now for threats that are still emerging. This is defence in depth by design, not defence by reaction. The organisations that treat cybersecurity as an ongoing investment — not a one-time compliance exercise — will be the ones still operating safely when the threat landscape shifts.
Synthesis
Cybersecurity in rail is a domain where the stakes are uniquely high. Unlike most industries where a breach means data loss, a rail cyber incident can mean physical danger, supply chain disruption, and national security risk. Australian rail’s rapid digitisation is creating operational benefits but simultaneously expanding the attack surface. The regulatory response (SOCI Act, ONRSR cyber requirements) is tightening, making cybersecurity compliance both a safety obligation and a legal requirement.
The connections to earlier themes are direct: data and analytics capabilities (Day 15) provide the monitoring foundation for detecting anomalous behaviour. The sustainability investments (Day 16) that drive IoT and cloud adoption simultaneously expand the attack surface. And the workforce skills gap (Day 12) is acute in cybersecurity, where specialised OT security talent is exceptionally scarce.
The uncomfortable truth: the same digital transformation that makes rail smarter makes it more vulnerable. Managing that paradox requires security architecture that’s as sophisticated as the operational technology it protects.
Vocabulary Spotlight
| Term | Definition |
|---|---|
| IT–OT convergence | Integration of Information Technology (business systems) and Operational Technology (train control, signalling, SCADA) networks, creating new cybersecurity attack surfaces |
| SOCI Act | Australia’s Security of Critical Infrastructure Act 2018 (amended 2022), mandating cybersecurity risk management for critical infrastructure including rail |
| Network segmentation | Dividing a network into isolated zones so a breach in one cannot spread to others, critical for protecting train control systems |
| Air gap | A physical isolation between a secure network and unsecured networks (including the internet), historically used to protect OT systems from cyberattacks |
| Ransomware | Malware that encrypts systems and demands payment for decryption, particularly dangerous when targeting safety-critical rail operations |
| NIST Cybersecurity Framework | A set of guidelines developed by the National Institute of Standards and Technology for managing and reducing cybersecurity risk, widely adopted for critical infrastructure protection |
| IEC 62443 | International standard series for industrial automation and control system (IACS) security, defining security levels and zones applicable to rail OT environments |
| Purdue Model | A reference architecture for industrial control systems that defines hierarchical network zones (Levels 0–5), used to design network segmentation strategies that isolate safety-critical rail OT from enterprise IT |
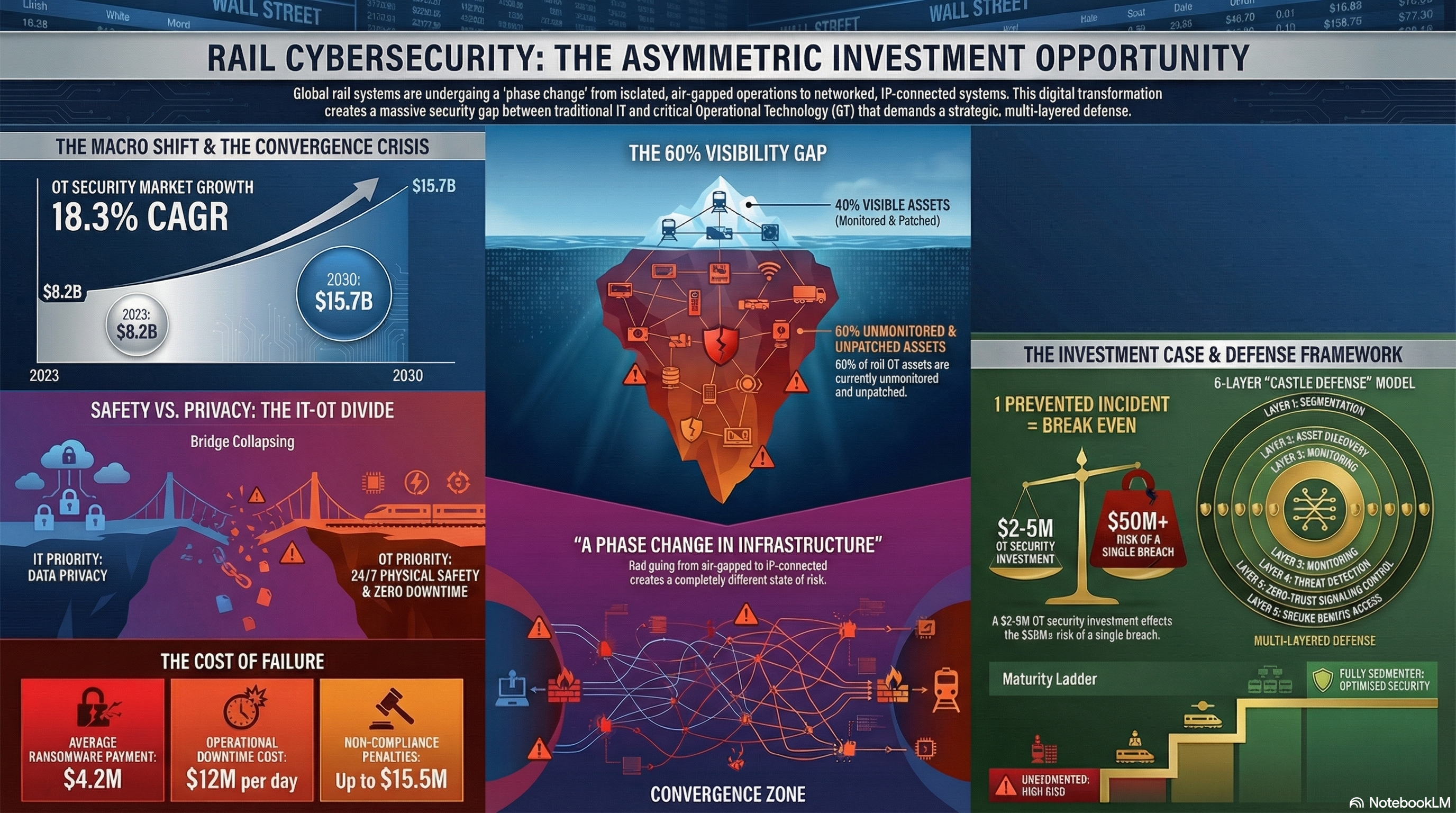
Micro Signal
Lynch Lens: The key micro-metric is “OT asset visibility” — what percentage of operational technology devices on a rail network are inventoried, monitored, and patched? The Dragos ICS/OT Cybersecurity Year in Review consistently finds that most industrial operators — including rail — can account for less than 60% of their connected OT assets. You can’t secure what you can’t see. The companies that solve OT asset visibility will own the rail cybersecurity market.
Macro Signal
Druckenmiller Lens: The macro trend is regulatory acceleration meets expanding attack surface. Every IoT sensor deployed, every cloud connection established, every ETCS digital signalling upgrade installed creates new attack vectors — while the SOCI Act and Essential Eight mandates tighten compliance requirements annually. Rail operators who treat cybersecurity as a one-time compliance exercise will face compounding risk. Those who invest in security by design — embedding cybersecurity architecture into every digital enhancement from inception — will avoid the catastrophic costs of retrofit and breach response. The macro bet: OT cybersecurity in critical infrastructure is a multi-decade growth sector, and the organisations that build capability now will define the standards everyone else follows.
In the News
The Australian Signals Directorate (ASD) releases new Essential Eight Maturity Model compliance guidelines for rail operators in early 2026, mandating patch management and multi-factor authentication for all train control and signalling systems within 12 months. This follows the ASD’s Annual Cyber Threat Report which identified critical infrastructure as facing escalating nation-state targeting.
Sources
| Type | Source |
|---|---|
| IBM | IBM Security — X-Force Threat Intelligence Index 2024: Transportation Sector Insights |
| IBM | IBM QRadar SIEM — “Threat Detection for IT and OT Environments” |
| IBM | IBM Institute for Business Value — “Securing Operational Technology in Transportation” (2024) |
| Government | Australian Cyber Security Centre — “Critical Infrastructure Cyber Security Assessment” |
| Government | Security of Critical Infrastructure Act 2018 — Legislation text |
| Industry | ONRSR — “Cyber Security in Rail Safety Management” |
| Standards | NIST Cybersecurity Framework — “Framework for Improving Critical Infrastructure Cybersecurity” (CSF 2.0) |
| Standards | IEC 62443 — “Industrial Automation and Control Systems Security” (ISA/IEC) |
| Standards | NIST Post-Quantum Cryptography — “Post-Quantum Cryptography Standardization” |
| Research | ENISA — “Railway Cybersecurity: Good Practices for the Railway Sector” |
| Research | Dragos ICS/OT Year in Review — “OT Cybersecurity Threat Landscape and Asset Visibility” |
| Regulation | CISA / TSA Security Directives — “Surface Transportation Cybersecurity Requirements” (US reference) |
| Incident | SecurityWeek — Danish Rail Cyberattack — “Cyberattack Causes Trains to Stop in Denmark” (2022) |
Next: A Tale of Four Railways · A familiar question — “how does Australia compare?” — leads to an unexpected discovery: no single country has it figured out.